The Poisoned Pipeline: Axios Supply Chain Attack
tl;dr
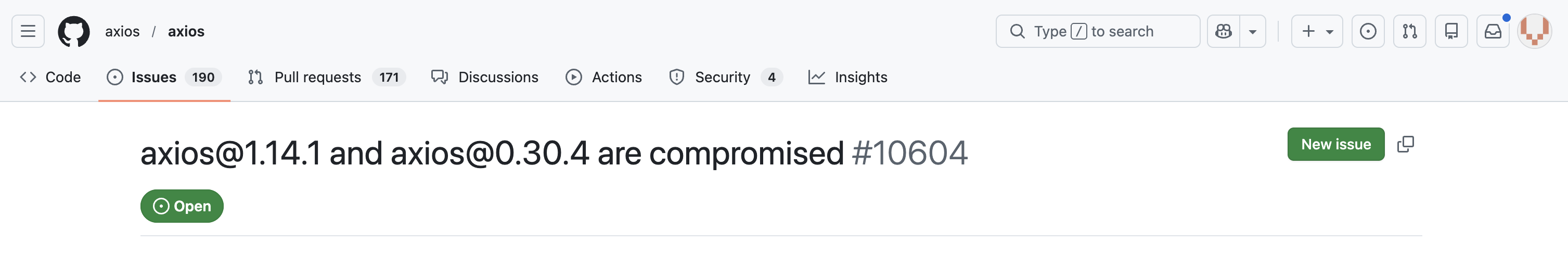
- Axios Supply Chain: Between 30-31 March 2026, a lead maintainer’s account was compromised to publish trojanized versions (1.14.1 and 0.30.4), introducing a dependency that deploys a multi-stage Remote Access Trojan (RAT).
- The Malware: The RAT targets Windows, macOS, and Linux, and can reside in memory to evade detection. Attacker-controlled accounts and supporting C2 infrastructure were created less than 24 hours before the attack, indicating deliberate pre-positioning and coordinated execution.
- Immediate Action: Block known C2 infrastructure, rotate all cloud and CI/CD secrets exposed to affected environments, and downgrade the package to a known safe version (1.40.0).
- The Bigger Picture: While Axios is the latest supply chain victim, the TeamPCP campaign since March 19 is targeting tools such as Trivy and KICS. These two attacks represent a systemic shift in supply chain risk, where the weaponization of trusted libraries and security tools has evolved into persistent access at scale.
Introduction
In the last two weeks, the software development ecosystem has moved into a state of crisis. We are witnessing a fundamental shift in how supply chain attacks are executed: the CI/CD pipeline is no longer just a target for theft; it is the entry point for large-scale supply chain compromises.
Instead of breaking into a production database, attackers inject malicious code into the tools (Trivy, KICS) or libraries (Axios, LiteLLM) that developers trust. As we have seen in recent supply chain attacks, threat actors are no longer just looking for data; they are hunting for the cloud secrets and tokens that live within these pipelines to leapfrog from a build runner directly into a cloud production environment. Because these tools often run with high privileges in CI/CD environments, a single poisoned update can compromise thousands of downstream organizations simultaneously.
This blog primarily focuses on the currently discovered and continuously developing Axios supply chain compromise.
The Timeline: Two Distinct Threats
While both recent attacks represent supply chain compromises, it is vital to distinguish between the ongoing TeamPCP campaign and the very recent Axios incident.
1. TeamPCP: Active since March 19, 2026
The TeamPCP campaign has continued to escalate since March 19, 2026 and should be treated as a sustained threat rather than a short term spike. The group appears organized and deliberate in its operations and, according to SANS Internet Storm Center, is now running dual ransomware campaigns.
Their activity goes beyond credential theft. TeamPCP is reportedly targeting high value enterprise data to support extortion. Recent reporting includes an alleged compromise of Databricks and the public release of data linked to AstraZeneca.
The group uses stolen secrets to move laterally across cloud environments, enabling broader access, data exfiltration, and potential ransomware deployment. While financially motivated, their operations are geared toward large scale corporate extortion.
2. Axios: Active since March 31, 2026
The Axios compromise, identified on March 31, 2026, is currently assessed as a separate event, despite sharing a supply chain delivery vector with other recent activity. The threat actor demonstrates a targeted and controlled approach by hijacking a lead maintainer’s npm account to publish malicious versions (1.14.1 and 0.30.4).
The threat actor introduced a cross-platform RAT. This indicates a focus on persistent access, enabling continued control over the compromised developer workstations or build environments beyond initial execution. However, the motivation remains undetermined, but the execution suggests a targeted intrusion rather than broad opportunistic abuse.
Open sources, particularly an Elastic researcher (@DefSecSentinel), has suggested that this RAT contains overlaps or similarities with the WAVESHAPER malware family. A piece of malware attributed to the DPRK-nexus threat actor, UNC1069. UNC1069 is assessed to be a financially motivated threat actor.
UPDATE: March 31, 2026 – 16:00 UTC
Fingerprinting the HTTP response headers, we identified a unique ETag: W/"16-zUIWjx30dNMOrJoqA1R8JWYnVAw" which is shared between the primary Axios C2 and 23.254.167[.]216; both servers are also hosted on Hostwinds LLC (AS 54290). This specific IP and ETag fingerprint provide a high-confidence link to the "JustJoin" landing pages. As documented by researchers at Hunt.io, this infrastructure is associated with DPRK-nexus activity. This overlap further supports that the Axios incident is likely linked to a DPRK-nexus threat actor.
Axios RAT Analysis
The trojanised Axios npm package delivers a cross-platform RAT across Windows, macOS, and Linux systems, indicating deliberate targeting of developer environments and build infrastructure. Once executed, the implant establishes a consistent C2 channel, beaconing every 60 seconds using base64-encoded JSON over HTTP POST. Notably, it uses a legacy User-Agent: mozilla/4.0 (compatible; msie 8.0; windows nt 5.1; trident/4.0), which refers back to Windows XP.
The malware enumerates high-value directories such as Documents, Desktop, and configuration paths, followed by continuous telemetry collection including running processes, hardware specifications, and system uptime. This enables operators to quickly profile and prioritize compromised systems.
On Windows, the RAT leverages reflective .NET loading to execute additional payloads directly in memory. This technique avoids writing binaries to disk, significantly reducing forensic visibility and increasing evasion against traditional detection mechanisms.
Persistence is both simple and effective. A registry run key named MicrosoftUpdate points to a batch script (system.bat). When the user account logs in where the registry was set, this script retrieves a fresh payload from the C2 server. This effectively turns persistence into a live update mechanism, allowing the threat actor to modify tooling and capabilities in real time.
Infrastructure analysis suggests additionally under reported C2 infrastructure. The malicious payload package plain-crypto-js was published by nrwise@proton[.]me, distinct from ifstap@proton[.]me, the account associated with the Axios maintainer compromise. Public key metadata indicates the latter was created less than 24 hours prior to the attack, pointing to staged account preparation.
Further Analysis of the C2 reveals that callnrwise[.]com sits on the same infrastructure as the primary Axios C2 domain, sfrclak[.]com. The naming similarity between the staging email (nrwise) and the secondary C2 domain (callnrwise) indicates a likely coupled operation.
Are we vulnerable?
Audit lockfiles to see whether the malicious versions (1.14.1 and 0.30.4) are included. For npm, the lockfile is titled package-lock.json, whereas pnpm uses pnpm-lock.yaml. Other package managers (i.e., Bun, etc.) follow a similar naming pattern to know which file is used as the lockfile.
Response
If confirmed vulnerable, validate whether the environment is compromised by searching for the IOCs as mentioned in the chapter ‘IOCs’. Quarantine impacted hosts to sever the connection with the C2 infrastructure and reset impacted sessions and accounts. It is also recommended to audit CI/CD pipelines and investigate the environment deployed to for traces of the malware.
Remediation
- Search package-lock.json, yarn.lock or pnpm-lock.yaml specifically for axios@1.14.1, axios@0.30.4, or plain-crypto-js.
- If a malicious version is found, then downgrade the package to a known safe version (1.40.0). If you can’t immediately update every sub-dependency, use the overrides (npm) or resolutions (yarn) field in your package.json to force Axios back to a safe version.
- Rotate secrets, tokens and keys. The payload includes a RAT capable of exfiltrating system data, assume all environment variables, SSH keys and tokens on the infected machine are assumed compromised and act accordingly by rotating these.
Prevention
- The Wait-and-See Defense: In the Axios attack, scanners flagged the malware in just six minutes, but susceptibility is still introduced in the window between a malicious upload and its removal from the registry. A way to remediate this is by implementing a minimum release age. Setting it to e.g. ‘min-release-age=7’ disallows including a new package when its release date is less than 7 days ago. This provides some delay, allowing for the public eye to audit the package before automatically including it in a production environment.
- Pin Your Versions: By default, npm uses the caret (^), which allows it to pull minor updates automatically.
IOCs
The following IOCs are associated with the Axios supply chain compromise, also available on our GitHub:
Additional File System Indicators
Windows
- %PROGRAMDATA%\wt.exe
- %PROGRAMDATA%\system.bat
- %TEMP%\6202033.vbs
- %TEMP%\6202033.ps1
- %TEMP%\<GUID>.ps1
- Key: HKCU\Software\Microsoft\Windows\CurrentVersion\Run
- Name: MicrosoftUpdate
- Value: %PROGRAMDATA%\system.bat
macOS
- /Library/Caches/com.apple.act.mond
- /tmp/.XXXXXX.scpt
- /private/tmp/.*
Linux
- /tmp/ld.py
About Invictus Incident Response
We are THE company for cloud incident response and we ❤️ the cloud. We specialize in supporting organizations in preparing and responding to a cyber attack. We help our clients stay undefeated!
🆘 Incident Response support reach out to cert@invictus-ir.com or go to https://www.invictus-ir.com/24-7
Be ready for the next cloud incident.

